Medibank’s information was compromised when cybercriminals targeted an individual with privileged access to this company’s private information. Cybercriminals sold this individual’s information to a bad actor who accessed the information of Medibank’s customers. After that, everyone with insurance through this company experienced a data breach.
Technique used
The Medibank hack began with the theft of credentials belonging to an individual with privileged access to Medibank’s internal systems. These credentials were sold and purchased on the dark web by a bad actor who used them to gain access to Medibank’s internal system.
Once inside, the bad actor identified the location of a customer database and used the stolen privileged credentials to write a script to automate the customer data exfiltration process – a similar data theft mechanism was used in the Optus data breach.
This stolen data was placed into a zip file and extracted through two established backdoors. Medibank’s security team allegedly detected suspicious activity at this point and shut down both backdoors, but not before 200GB of customer data was stolen,
9.7 million Medibank customers were impacted by the breach. Compromised records include:
- Names
- Birth dates
- Passport numbers
- Information on Medicare claims
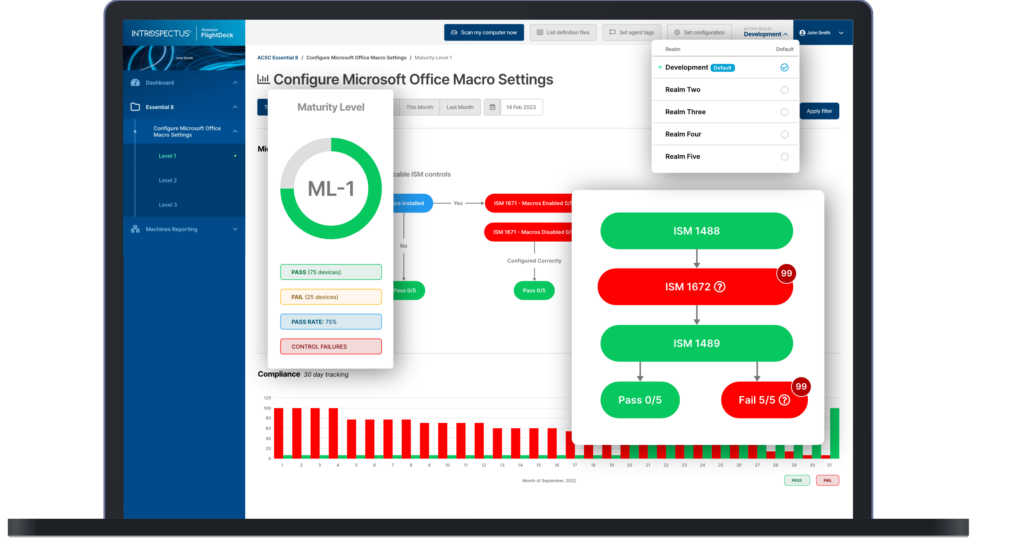
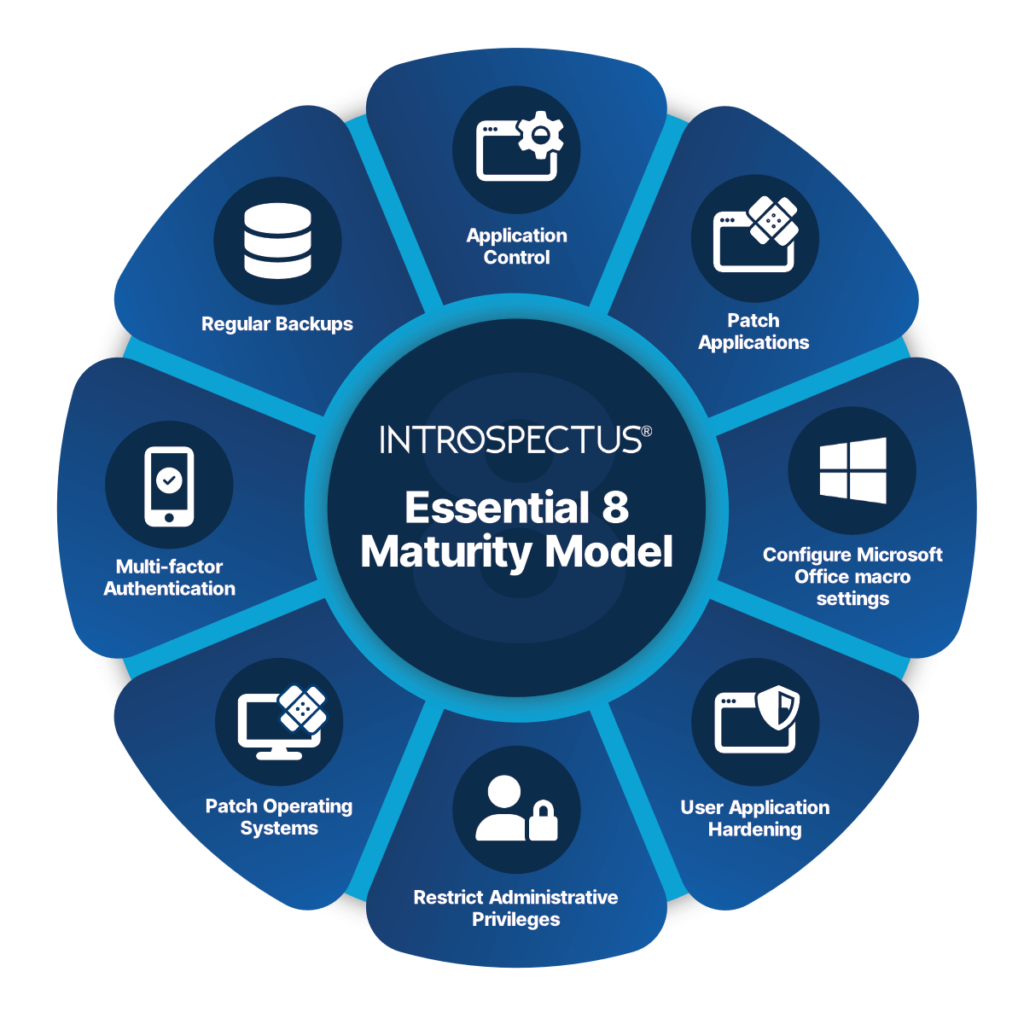
Essential Eight Mitigations
A number of controls in the Essential Eight will prevent against this type of attack including but not limited to:
- ISM 1387 – Administrative activities are conducted through jump servers.
- ISM 1649 – Just-in-time administration is used for administering systems and applications.
- ISM 1689 – Privileged accounts (excluding local administrator accounts) cannot logon to unprivileged operating environments.
- ISM 1173 – Multi-factor authentication is used to authenticate privileged users of systems.