Products
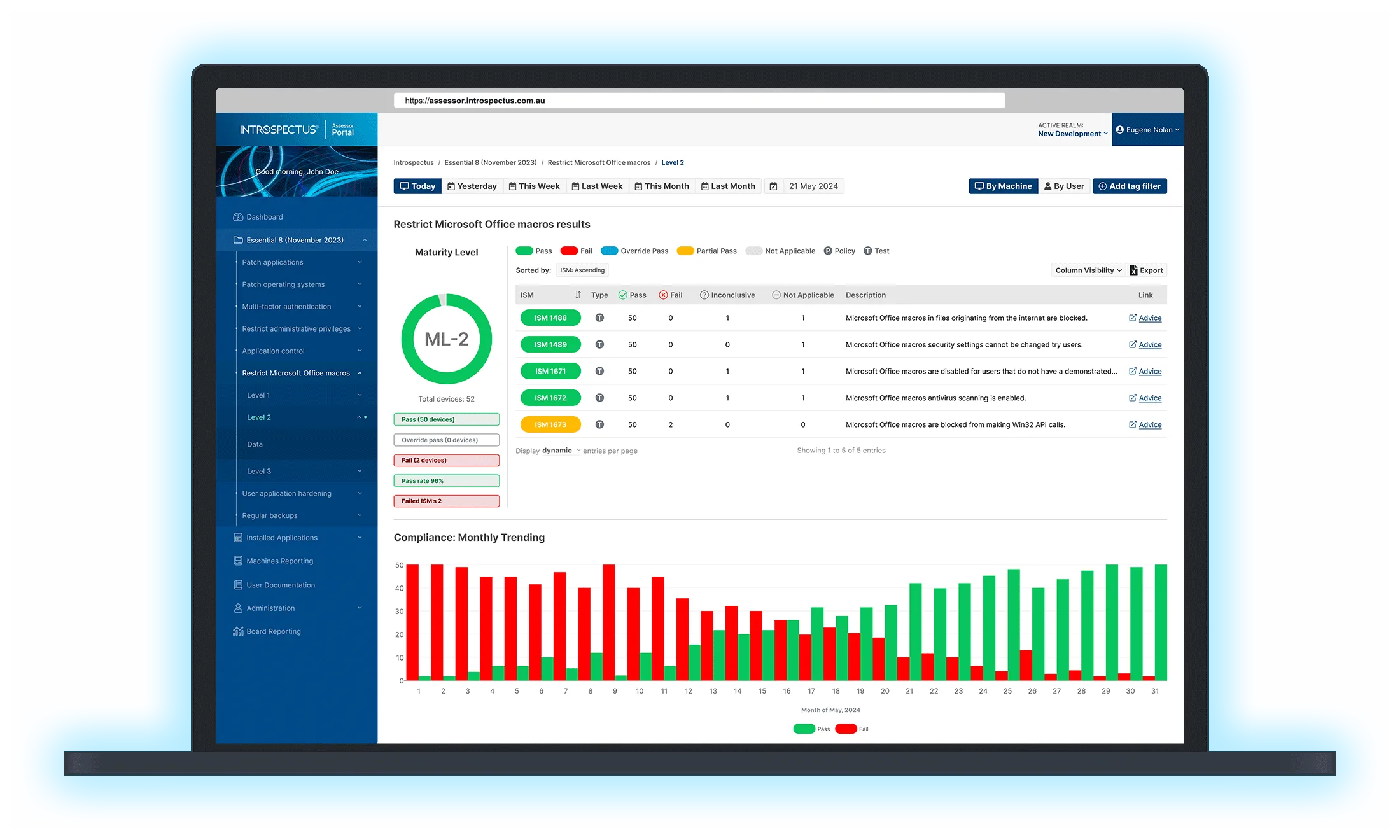
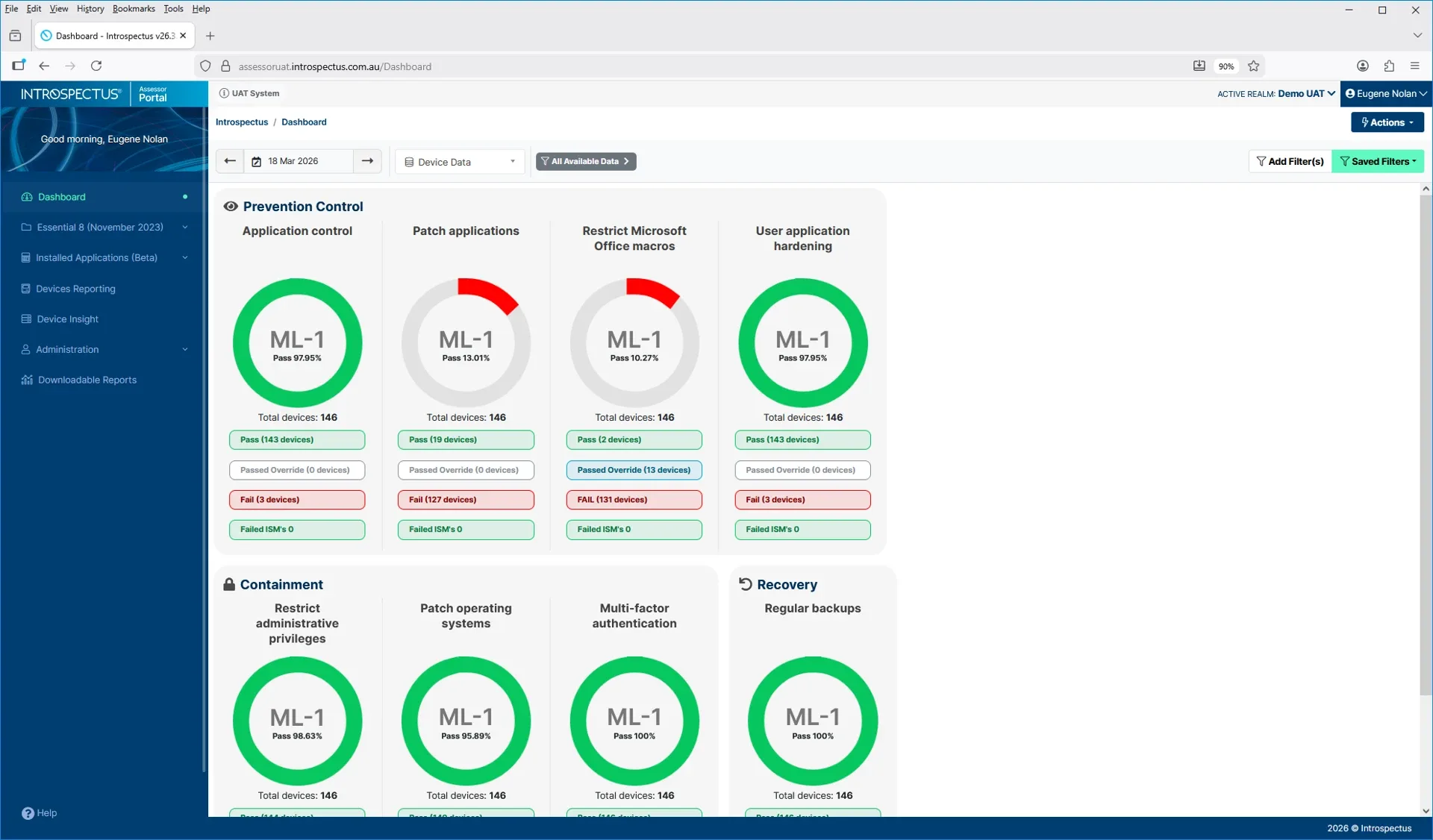
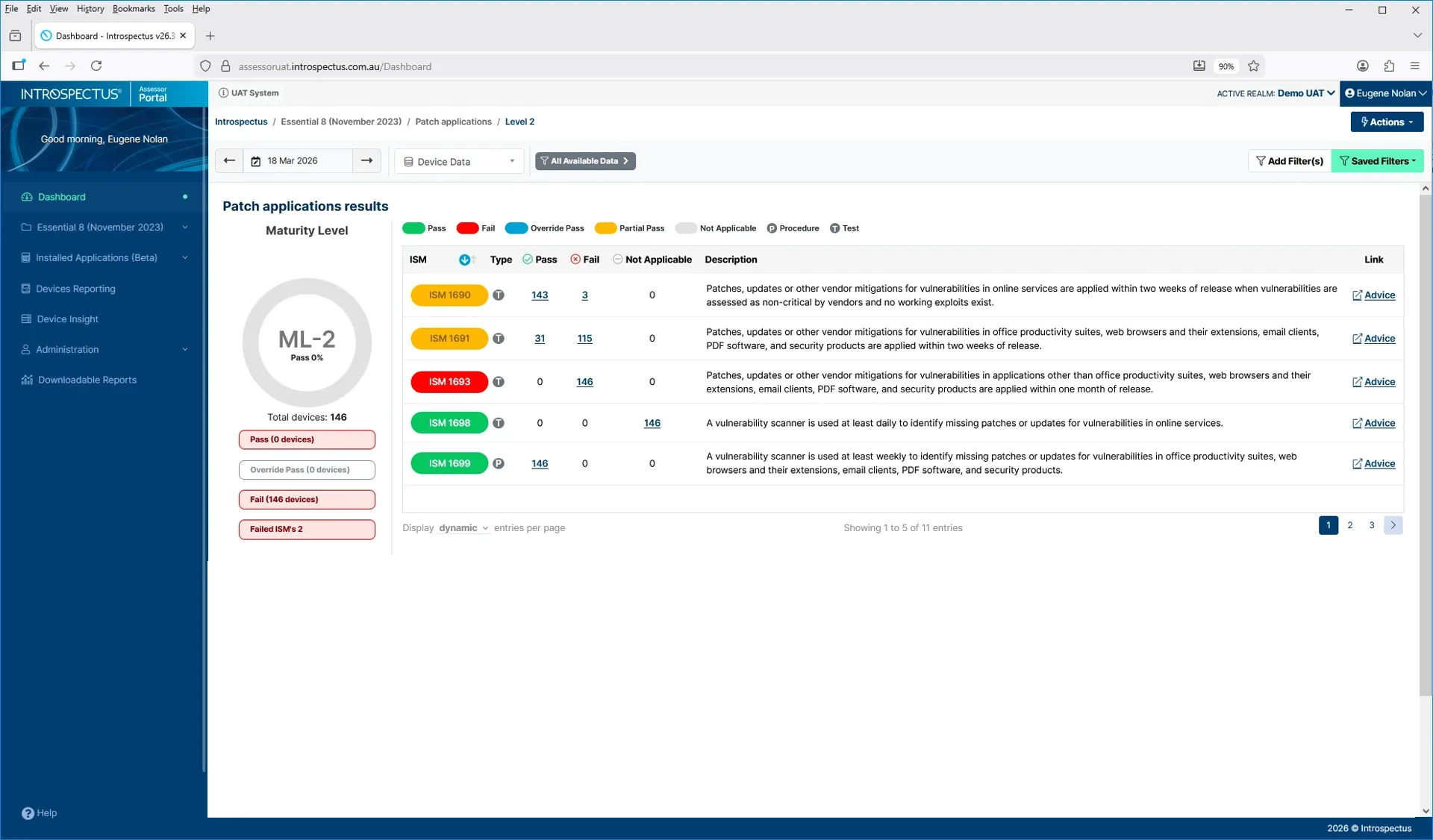
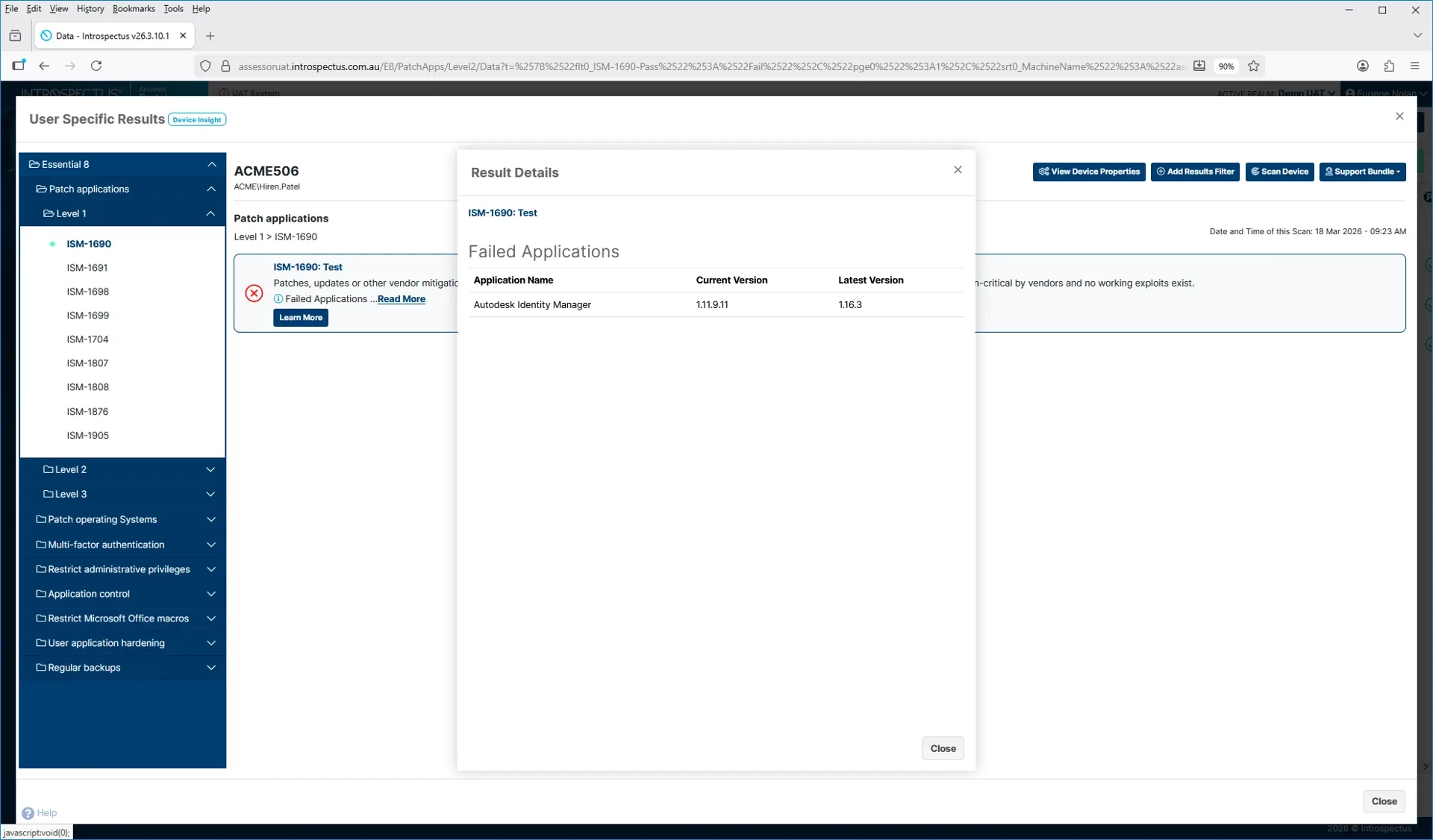
Essential Eight Cybersecurity Strategies
Introspectus provides real time, analytical information about your IT environments so that you can make data-driven decisions.