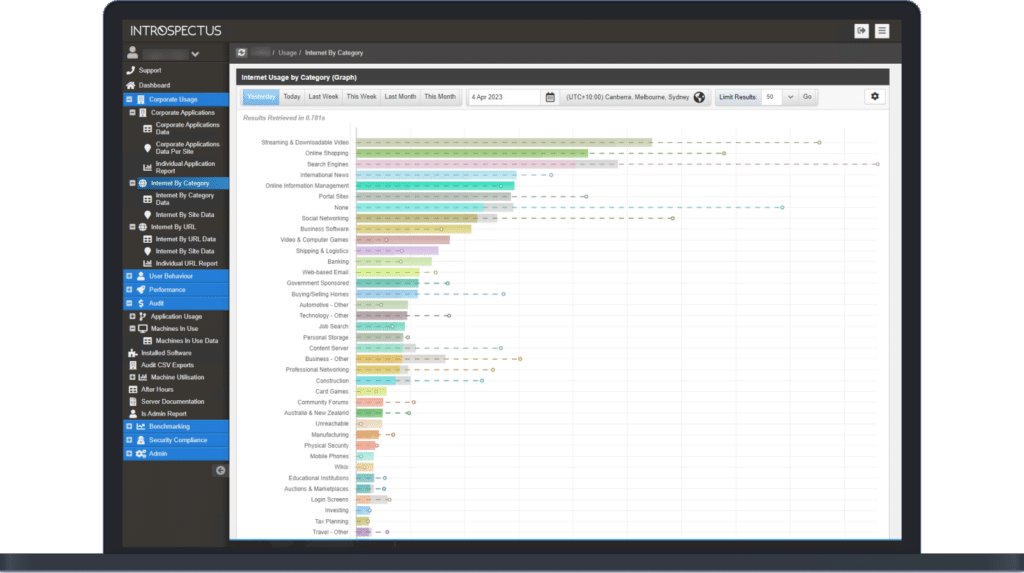
What is Internet Usage Tracking?
Internet Usage is a measure of how long users in your organisation spend on the Internet as part of normal day-to-day activities.
Existing internet reporting tools provide statistics of internet usage based on downloads or the number of times a user visits a website. These tools assess a user’s interaction with the internet by broadly looking at all browser activity, whether active or dormant, and incorrectly assume that web traffic is being generated even if the browser is not being used.
Organisations can incorrectly assume that a staff member was on social media all day when in reality the staff member looked at social media at the start of the day and minimised the web browser instead of closing the browser. Due to the design of social media websites and current reporting tools, the web browser in its minimised state keeps updating existing tools, generating large amounts of traffic and therefore incorrectly reporting that the staff member was using social media all day.