What is HR Reporting and how does it work?
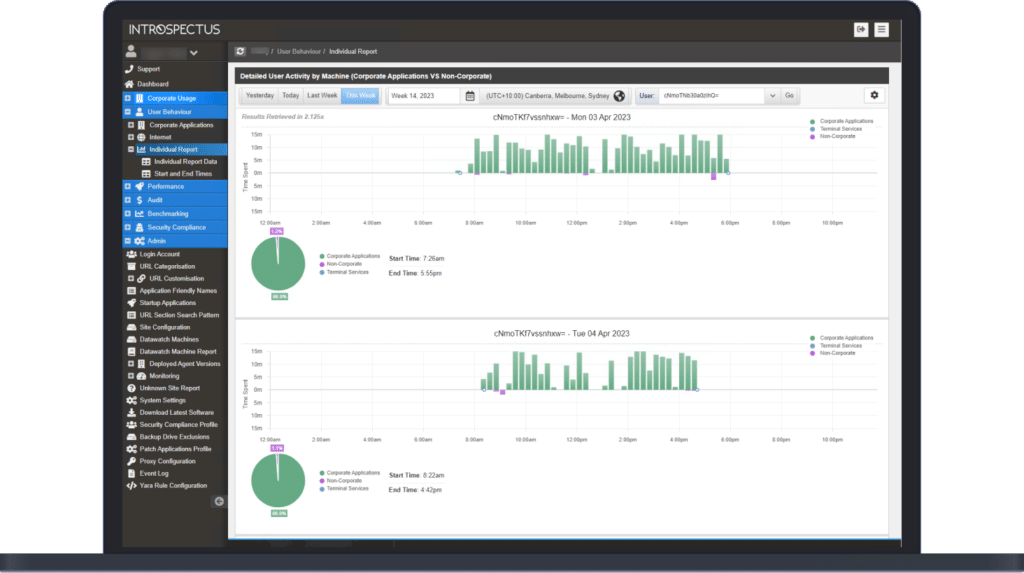
Current Human Resources (HR) reporting tools require company staff to correctly record the start and end times of each day. This is often manually recorded at the end of each week or fortnight and may be difficult to compile retroactively.
Timekeeping software, if used, may need to be dedicated to workstations or specifically invoked to record a timestamp.
Time spent working away from the office, after hours or on weekends, is not recorded or may be overstated.